PSD2 versus 3DS2: EU security regulations explained

3D Secure 2.0 (3DS2) is a globally accepted security protocol that was designed to protect credit card information from unauthorized use online. Essentially, it adds a layer of authentication to online credit and debit transactions.
The purpose of 3DS2 authentication is to verify a cardholder’s identity before a business authorizes a transaction. That way, the business can reduce online fraud, comply with international regulations, and increase cardholder confidence in digital transactions.
3DS2 meets Strong Customer Authentication (SCA) requirements under the second Payment Services Directive (PSD2).
There’s a lot to unpack with these regulations, so let’s take a closer look at PSD2 versus 3DS2 regulations and the challenges that 3DS2 regulations present to businesses.
PSD2 versus 3DS2: What is PSD2?
PSD2 is the second iteration of a European Union directive to regulate payment services and payment service providers. It requires businesses and issuing banks to have stronger fraud prevention checks. The directive, introduced in 2007, was designed to make payments safer, increase consumer protection, bolster international e-commerce, and help third-party financial service companies scale.
PSD2 affects businesses, issuers, and consumers differently. Consumers benefit from increased security and data protection. But issuers and businesses face new challenges by meeting PSD2 regulation compliance. In particular, the directive requires banks to have open APIs and meet SCA requirements.
Open APIs allow new players to access bank accounts with consumer consent. New players must be registered, licensed, and regulated. But once they are, they can access consumer payment accounts to make payments and credit transfers on the consumer’s behalf and provide account summaries.
The goal of SCA is to reduce fraud by requiring businesses and issuers to validate consumers when they use electronic payment methods in the European Economic Area. SCA requires at least two of three independent authentication elements for all electronic transactions.
- Knowledge: Something you know (e.g., your PIN)
- Possession: Something you have (e.g. your card)
- Inheritance: Something you are (e.g. biometric identifiers)
Transaction Risk Analysis (TRA) exemptions
SCA reduces the risk of fraud and protects customer data. But it also adds significant customer friction and disrupts the payment process. However, TRA exemptions allow low-risk transactions to bypass SCA requirements. Low-risk transactions must pass a robust risk analysis or fraud screening, which accounts for:
- Abnormal spending or payer behavioral patterns
- Unusual information about the payer’s device
- Malware infections throughout the authentication procedure
- Known fraud scenarios in the provision of payment services
- Abnormal payer locations
- High-risk payee locations
When was 3DS2 created?
Visa and Mastercard created 3DS2 jointly in October 2016 to update 3DS regulations. EMVCo owns the specifications, which are overseen by EMVCo’s six member organizations: American Express, Discover, JCB, Mastercard, UnionPay, and Visa. Each brand has adopted the current 3D secure protocol, but each has branded it differently (i.e., Verified by Visa, Mastercard SecureCode, and American Express SafeKey).
3DS2 is promoted as a solution for SCA that satisfies PSD2 requirements in Europe. But it can also be used on its own outside of Europe for customer authentication. In Canada, the deadline to enforce SCA and 3DS2 requirements is 2021. The European SCA requirement dictates that electronic payment services are secure and businesses have authenticated buyers safely and reduced fraud risks.
How does 3DS2 work?
3DS2 allows payment providers to send 150 data points, including device and order history, to a customer’s bank, so the bank can determine if the purchaser is the actual cardholder. The additional data helps the bank passively authenticate the cardholder, rather than asking the purchaser for a password every time.
If the data provided matches the bank’s requirements, the transaction can continue without friction or customer input. If input is required, then customers have more ways to authenticate themselves, including by thumbprint, app-based authentication, or one-time password.
When 3DS2 is used for authentication, the chargeback liability shifts from the business to the issuer. For example, if a lost or stolen card is successfully used to complete a transaction where 3DS2 is in place, the liability shifts from the business to the card issuer.
6 challenges with 3DS2 authentication
The liability shift makes 3DS2 authentication, including compliance with PSD2, beneficial. But 3DS2 has challenges that businesses should be aware of.
1. It only protects against fraud pre-authorization: 3DS2 protects fraud at the point of payment. It doesn’t protect against friendly fraud, policy fraud and promo abuse, or chargebacks from merchant errors. Fraud risk is high throughout the customer journey, pre- and post-authorization
2. The liability shift is limited: The liability shift for 3DS2 is limited to certain instances of fraud and occurs only in the case of fraudulent chargebacks from stolen or counterfeit cards. The liability shift doesn’t cover friendly fraud, refund and return fraud, marketing affiliate fraud, or loyalty fraud.
3. It doesn’t stop disputes and chargebacks: While 3DS2 can prevent some fraud use cases, it doesn’t stop customer disputes and the resulting chargebacks. The liability shifts from the business to the issuer. But card brands can still penalize businesses with excessive chargebacks and place them in fraud monitoring programs. Programs include Visa’s dispute monitoring program and MasterCard’s Chargeback Monitored Merchant program. Each program has strict requirements for getting out and subjects businesses to additional fees.
4. It comes with additional fees: 3DS2 authentication is not free. Each card issuer has a fee structure for their 3DS2 protocol. Fees are established on a transaction basis or a percentage of a transaction.
5. Not everyone follows protocol: Larger, more established card brands have adopted 3DS2 protocols. But newer fintech payment providers and smaller card brands aren’t guaranteed to use it.
How Kount can help with compliance regulations
3DS2 is an improvement over 3DS to protect transactions, but it doesn’t replace the need for a fraud prevention solution. And even though not all countries have fully adopted these requirements, all businesses can prepare for 3DS2 with a robust fraud prevention solution. Kount’s AI-driven digital fraud solution can solve 3DS2’s limitations by protecting the entire customer journey from known and emerging fraud trends.
By combining Kount’s industry-leading fraud prevention with 3DS2 payment authentication, businesses can remain compliant with fraud threshold rates and take advantage of the liability shift. They can also reduce overall costs by minimizing the frequency of 3DS2 authentication to further reduce false positives, manual reviews, and chargebacks.
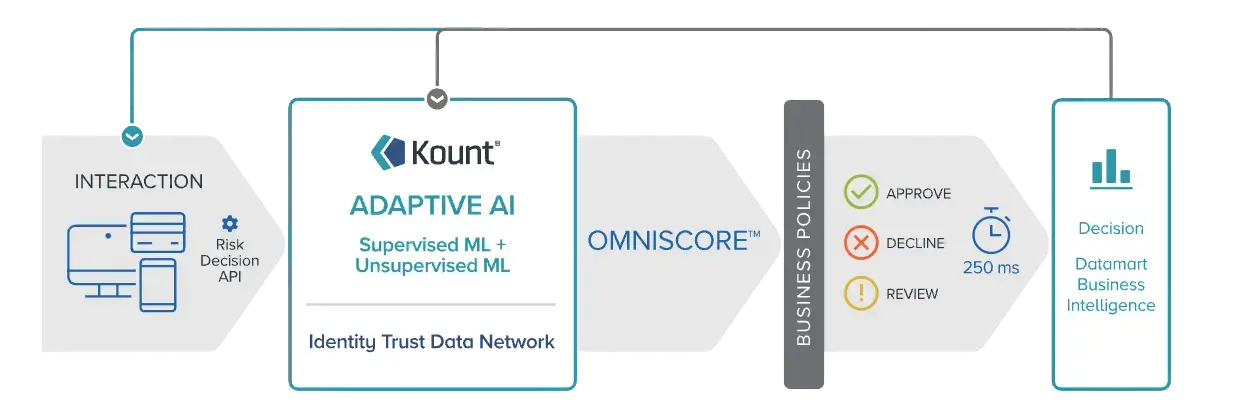
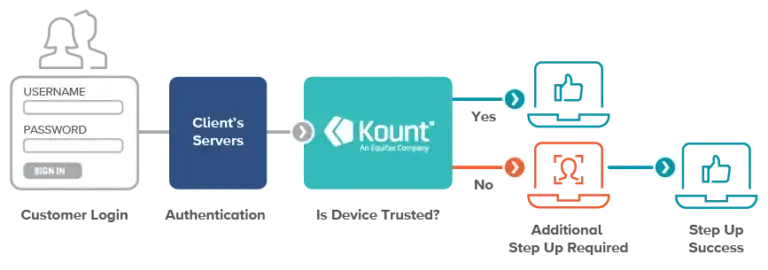
Kount can help businesses take advantage of TRA exemptions and avoid SCA where possible. PSD2 requires robust risk analysis that can detect abnormal spending, behavioral patterns, and information about the payer’s device. Kount’s account takeover solution can recognize abnormalities through Trusted Device and IP Risk capabilities.
Trusted Device stores information about the user and their devices, noting whether a device has been seen before and is trusted. IP Risk identifies risky logins where credentials don’t match an identity. If the IP risk is high, Kount challenges or blocks the device. Meanwhile, multi-dimensional velocities look at variables to identify network locations, devices, and accounts.
Finally, Kount integrates with dispute and chargeback management solutions from major card brands to help businesses intercept and deflect disputes. Managing dispute inquiries and chargebacks alerts from a single Kount dashboard can help businesses relay transaction details to stop friendly fraud automatically.
Businesses can also use chargeback notifications to stop shipments and prevent inventory loss. They can even use information about incoming chargebacks to adjust fraud policies and prevent similar chargebacks in the future.